With the news that automated rotation of keys is now available in preview in Azure Key Vault, I tested the configuration and notification options. Key rotation used to require a manual process, an API call, or an automation script using a combination of Azure Event Grid and an Azure Function app.
Azure Key Vault settings
First, you need to take note of the permissions needed for the person who is configuring the rotation policy. The documentation states the Key Vault Administrator role is sufficient, using Azure’s Role Based Access Control (RBAC). However, by default an Azure Key Vault will use Vault Access Policies. With a brand new test Key Vault, my user account didn’t receive the Rotate, Set Rotation Policy and Get Rotation Policy key permissions, so I had to browse to Access policies and select them. This follows the least-privilege principle of security so I don’t mind having to manually turn them on.

If you don’t catch this first, you’ll see the error “The operation “Get Rotation Policy” is not enabled in this key vault’s access policy”.

Rotation Policy configuration options
When I generate a new key in Azure Key Vault, I now see “Set key rotation policy (preview) Not configured” as the last option on the "Create a key" screen.

Clicking on the "Not configured" words (hyperlinked in blue) opens the Rotation policy (Preview) pane:
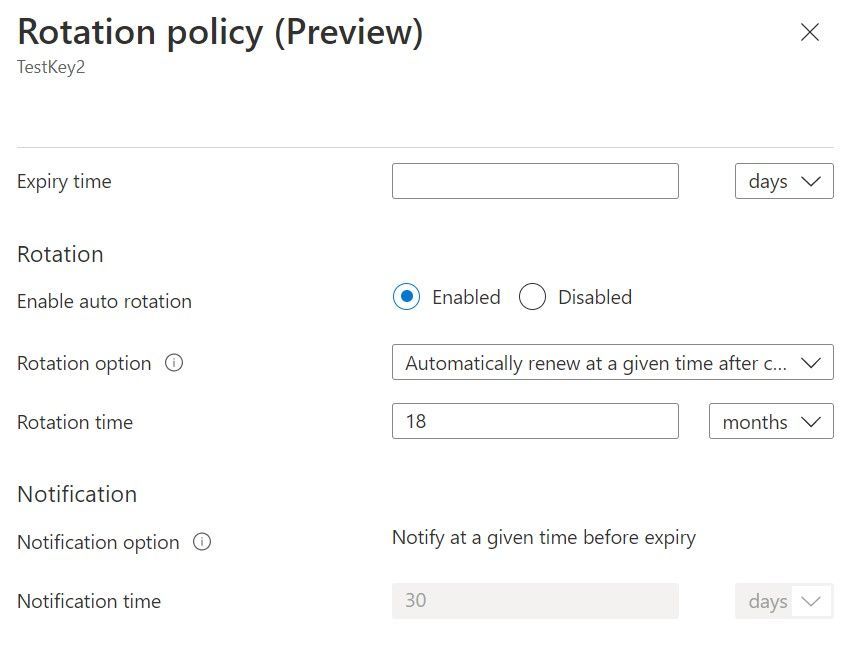
With the Expiry time blank, I can enable automatic rotation of the key for a certain number of days, months or years after the creation date of the key, but that must be a minimum of 7 days after creation.
If I add an expiry time, I also get the option to instead renew at a certain time before that expiry date, with a minimum of 7 days before expiry.
And, I can set a notification of x days before the key hits that expiry date, again with a minimum of 7 days. This triggers a notification into Azure’s event grid.
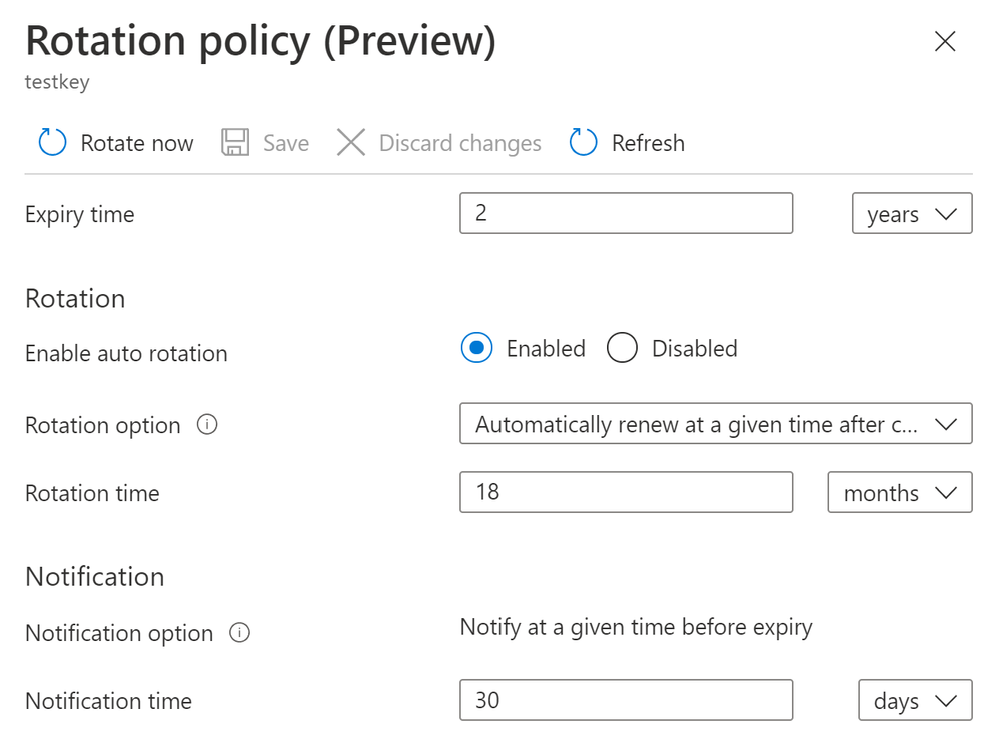
Your rotation policy can also be configured using the Azure CLI or in an ARM template, as long as the deployment executes with the Key Vault Contributor role.
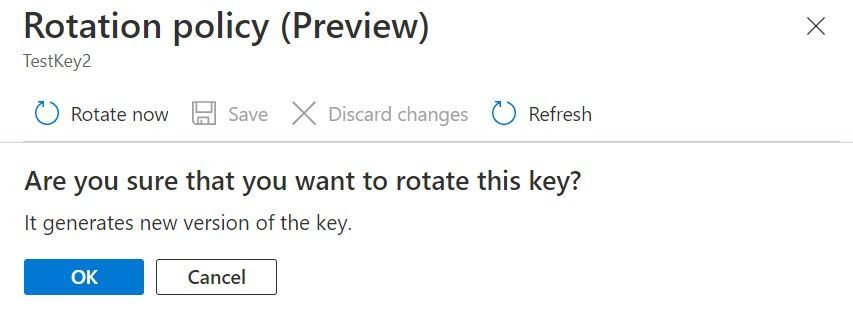
Finally, I can go into any key and select Rotate Now in the key’s Rotation Policy settings, to generate a new version of the key.
Currently you have to go into each key to see it’s retention policy configuration. It would be nice to have an indication on the main Keys blade as to which keys have retention policies configure and which keys don’t, but that would require the Get Retention Policy vault access policy which not all of your key vault users may have.
I do like that I can give someone access to use the rotate keys function independent of whether they can view or set retention policies (or vice versa).
Key expiry notification
While the key expiry notification seems very basic in the rotation policy configuration, it’s simplicity opens up a big range of possibilities. The notification creates an event in Azure Event Grid at the configured time, and from there we can trigger any of the Event Grid event handlers, such as Azure Functions, Logic Apps, Azure Automation or WebHooks.
Microsoft Cloud Solution Architect Brandon Rohrer has a great post on Sending Azure Management Events to a Teams Channel which would likely work with this scenario, but I need to wait 7 days for my event to trigger before I can test it!
Whether it’s a notification or ticket in another system, or some kind of automation, the event grid source is a great extensible platform to build a solution on that fits (or enhances) your business processes.
Learn more
Configure key auto-rotation in Azure Key Vault (preview)
Configure and manage secrets in Azure Key Vault
Posted at https://sl.advdat.com/33OOIcz