Microsoft Sentinel is a cloud native SIEM solution that allows you to detect and hunt for actionable threats. Microsoft Sentinel provides a rich variety of ways to import threat intelligence data and use it in various parts of the product like hunting, investigation, analytics, workbooks etc.
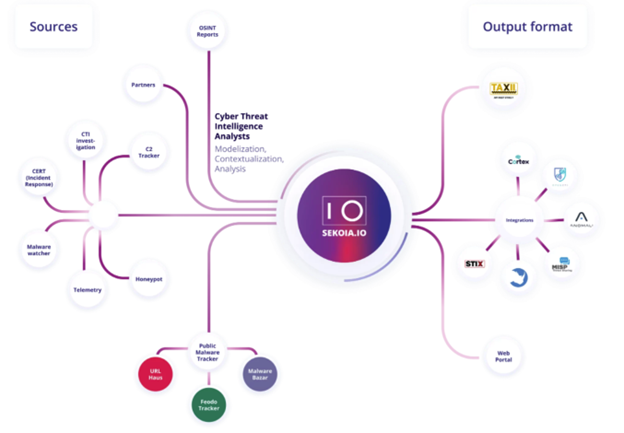
Cyber threat intelligence is the new oil of cybersecurity: if SIEM are engines, CTI is the fuel that makes you faster than attackers. It is now time to move from crude oil (raw streams of IOCs) to jet fuel: using intelligence to describe precisely how threats occur and get a bird’s eye view of your threat landscape.
Microsoft Sentinel was one of the early adopters of STIX/TAXII as the preferred way to import threat intelligence data. Microsoft Sentinel has built a data connector called the “Threat Intelligence -TAXII” connector that uses the TAXII protocol for sharing data in STIX format. This data connector supports pulling data from TAXII 2.0 and 2.1 servers. The Threat Intelligence – TAXII data connector is essentially a built-in TAXII client in Microsoft Sentinel to import threat intelligence from TAXII 2.x servers.
Today we are announcing the availability of the SEKOIA.IO Cyber Threat Intelligence into Microsoft Sentinel using the TAXII data connector.
SEKOIA.IO CTI for Microsoft Sentinel users
Because both Microsoft Sentinel and SEKOIA.IO speak in standard languages (STIX 2.1 and TAXII 2.1), the integration is completely transparent for customers, and the benefit is huge. Sentinel users who are also SEKOIA.IO CTI customers can really benefit from this top-quality threat intelligence by activating it in their environment. By bringing together the technology built by Microsoft within Microsoft Sentinel and powering it with the world class threat intelligence produced by SEKOIA, Sentinel users will be able to steadily reinforce their security posture.
Connecting SEKOIA.IO to Microsoft Sentinel
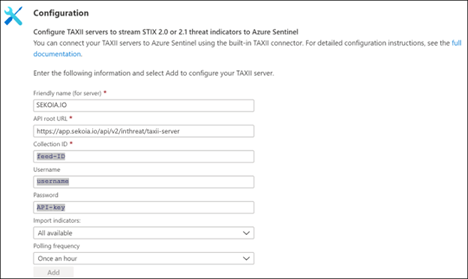
Email SEKOIA (microsoft.sentinel@sekoia.com) to get the credentials to access this CTI feed. To connect SEKOIA.IO CTI feeds to Microsoft Sentinel, you would need the API root URL, Collection ID and credentials of the SEKOIA.IO TAXII server.
The full procedure for setting a SEKOIA.IO TAXII feed for Microsoft Sentinel can be found here.
For more details on how to configure the TAXII data connector in Microsoft Sentinel, please refer to the following documentation.
Once you import threat intelligence data from SEKOIA.IO into Microsoft Sentinel it shows up in the ThreatIntelligenceIndicator table of log analytics. The data also shows up in the Threat Intelligence menu in the product where you can search, sort, filter, and tag on the data.
Put SEKOIA threat intelligence to use in Microsoft Sentinel
Once the threat intelligence from SEKOIA.IO is imported into Microsoft Sentinel, you can use it for matching against log sources. This can be done using the out-of-the-box analytic rules in Microsoft Sentinel. These completely customizable analytics rules used to match threat indicators with your event data all have names beginning with, ‘TI map’.
To learn how to enable and create analytic rules, follow the steps mentioned in this documentation.
Posted at https://sl.advdat.com/3kXtA9nhttps://sl.advdat.com/3kXtA9n